by CPI Staff | Apr 30, 2026 | Blog, Cloud Security, Cyber Security Strategy & Governance, Cybersecurity, Entra ID, Essential 8, Microsoft 365, Microsoft 365 Security, Microsoft Intune, Microsoft Purview
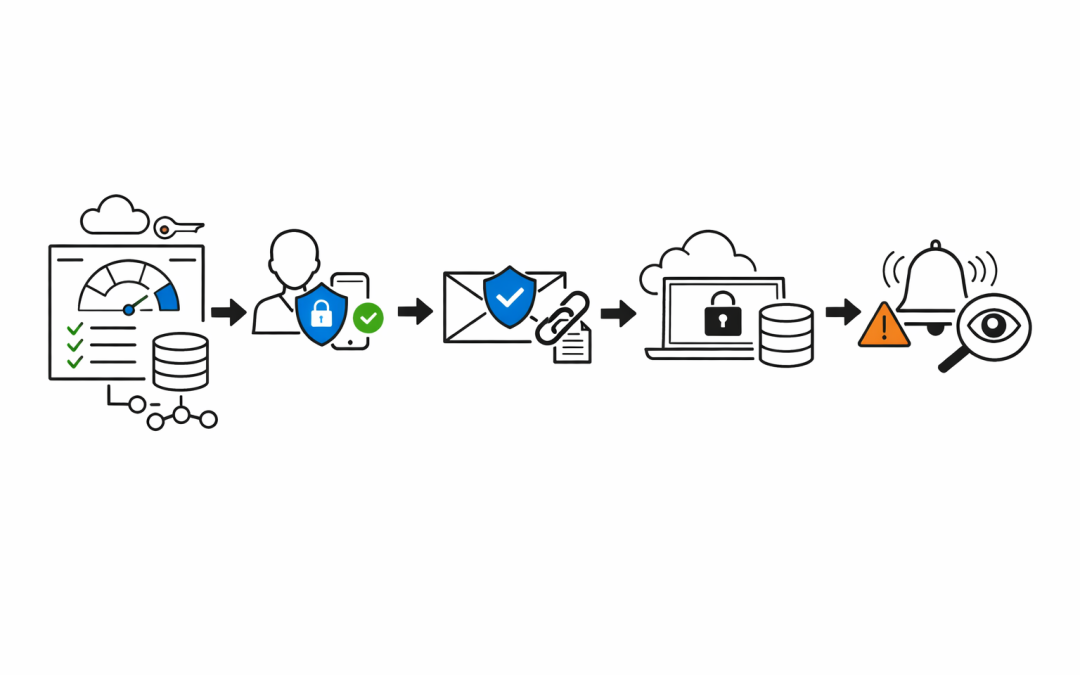
Small businesses are not small targets. Threat actors know that organisations with fewer than 50 staff rarely have a dedicated security team. They know Microsoft 365 is the backbone of most Australian SMBs — email, files, Teams, identity. And they know most of those...

by CPI Staff | Apr 30, 2026 | Blog, Cloud Security, Cybersecurity, Entra ID, Essential 8, Microsoft 365, Microsoft 365 Security
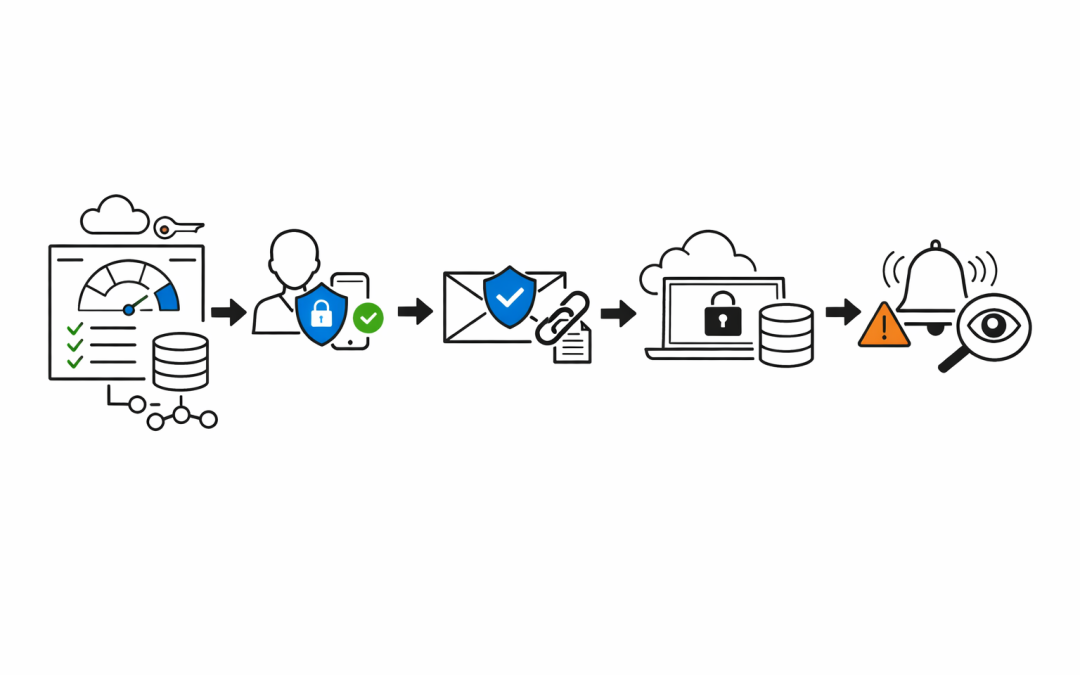
Every Microsoft 365 tenant tells a story. Emails flowing, Teams meetings running, SharePoint humming along. From the outside, everything looks operational. But operational is not the same as secure — and the gap between those two things is where breaches happen. When...

by CPI Staff | Apr 30, 2026 | Blog, Cybersecurity, Microsoft 365, Microsoft 365 Security, Microsoft Intune
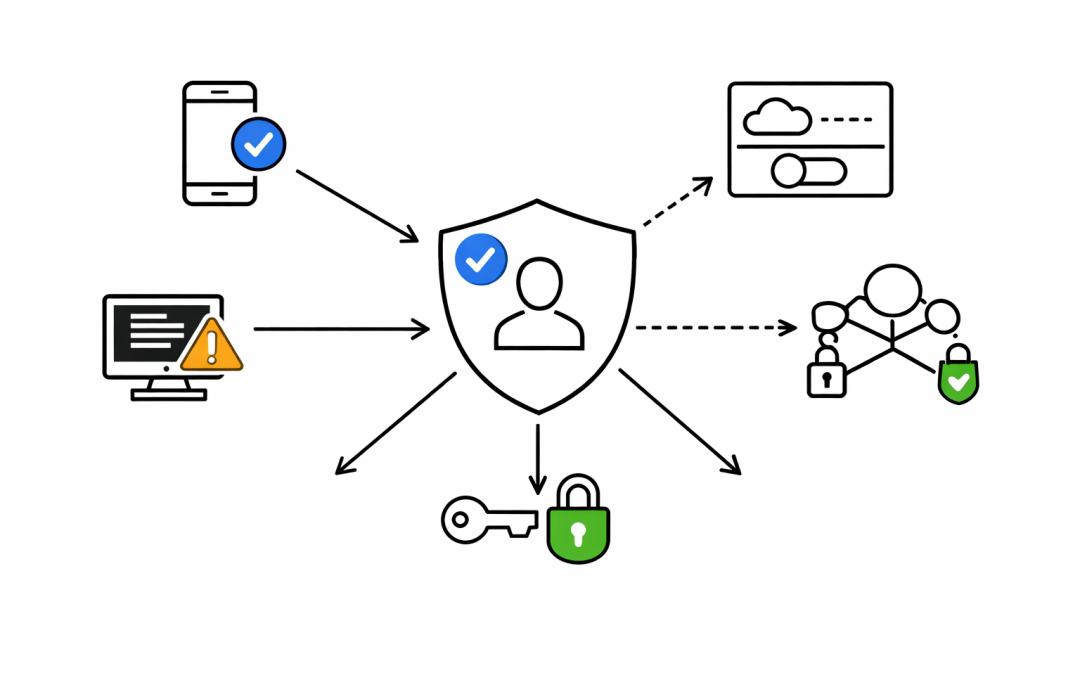
Most Australian organisations have invested in Microsoft 365 licences, security policies, and compliance controls. But there is a gap that regularly gets overlooked — and attackers know exactly where it is. Unmanaged devices. A personal laptop, a contractor’s...

by CPI Staff | Apr 29, 2026 | Blog, Cloud Security, Cybersecurity, Microsoft 365
When our team starts a Microsoft 365 security review, we focus on the areas that quickly tell us whether an environment is well controlled, loosely managed, or quietly carrying avoidable risk. For many Australian organisations, Microsoft 365 has become the centre of...

by CPI Staff | Apr 24, 2026 | Blog, Microsoft 365, Microsoft Intune, Windows 365
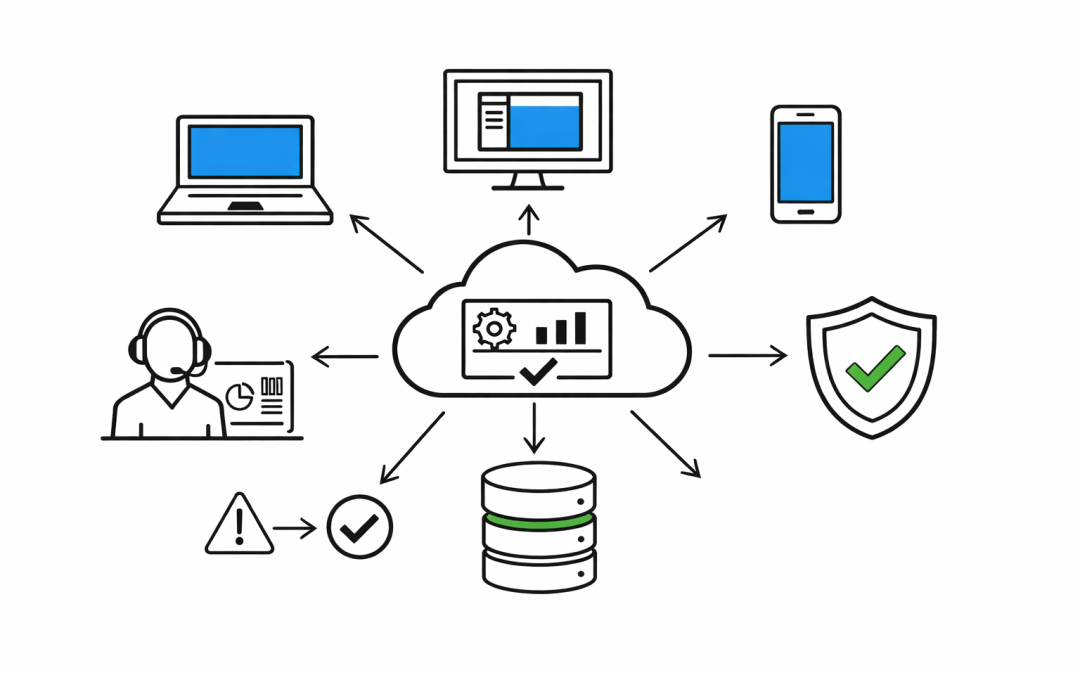
Too many IT teams are still managing endpoints through three different operating models at once. Physical laptops sit in one stack, remote access sits in another, and virtual desktops sit somewhere else again. That fragmentation is expensive. It slows onboarding,...