by CPI Staff | May 28, 2026 | AI for Business & AI Strategy, AI Governance & Risk Management, AI Vendor Selection & Implementation, Blog
AI agents are moving quickly from interesting demos to practical business tools. But many organisations run into the same limitation once they start testing them in real workflows: the agent forgets. It forgets the customer context from the last interaction. It...

by CPI Staff | May 28, 2026 | AI Governance & Risk Management, Blog, C#
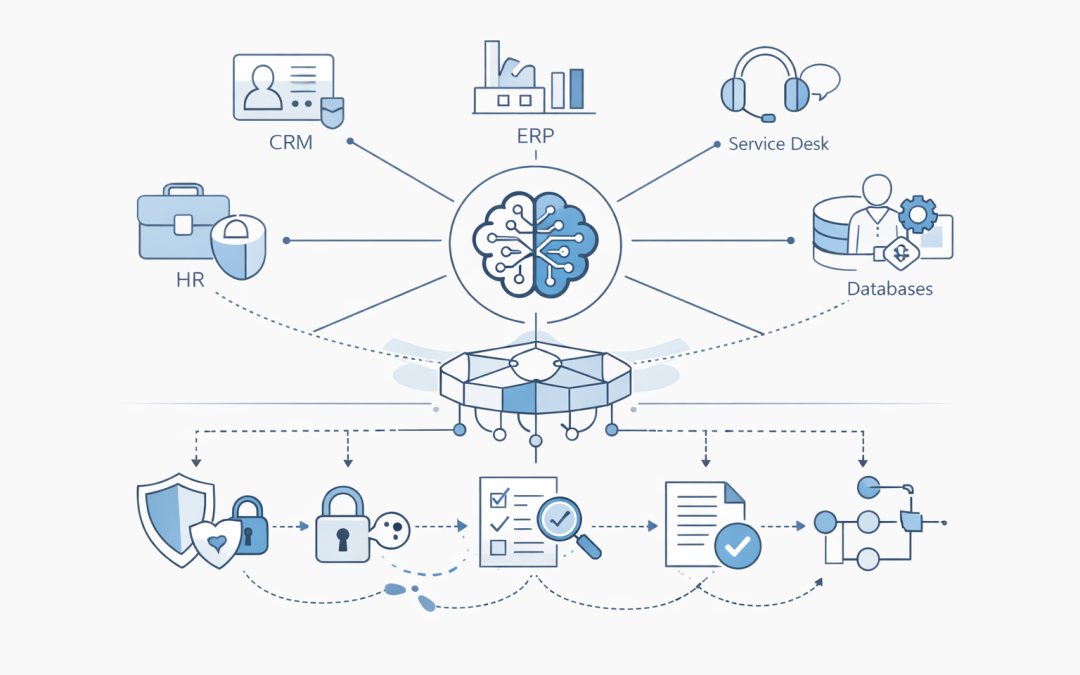
AI agents are moving from demos into production workflows. They can read documents, call APIs, query databases, create tickets, summarise customer history, and trigger business processes. That power creates a new infrastructure problem for Australian organisations: an...

by CPI Staff | May 28, 2026 | AI for Business & AI Strategy, AI Governance & Risk Management, Blog, C#
AI agents are moving from proof of concept to production planning. For many Australian organisations, the question is no longer whether an agent can answer a question. The harder question is whether it can safely do useful work across the systems the business already...

by CPI Staff | May 28, 2026 | AI for Business & AI Strategy, AI Governance & Risk Management, AI Vendor Selection & Implementation, Blog
AI agents are moving quickly from proof-of-concept demos into real business workflows. For Australian organisations, the question is no longer whether agents are interesting. The question is how to build them in a way that is secure, supportable, cost-aware, and...

by CPI Staff | May 14, 2026 | Blog, Cybersecurity, Microsoft 365
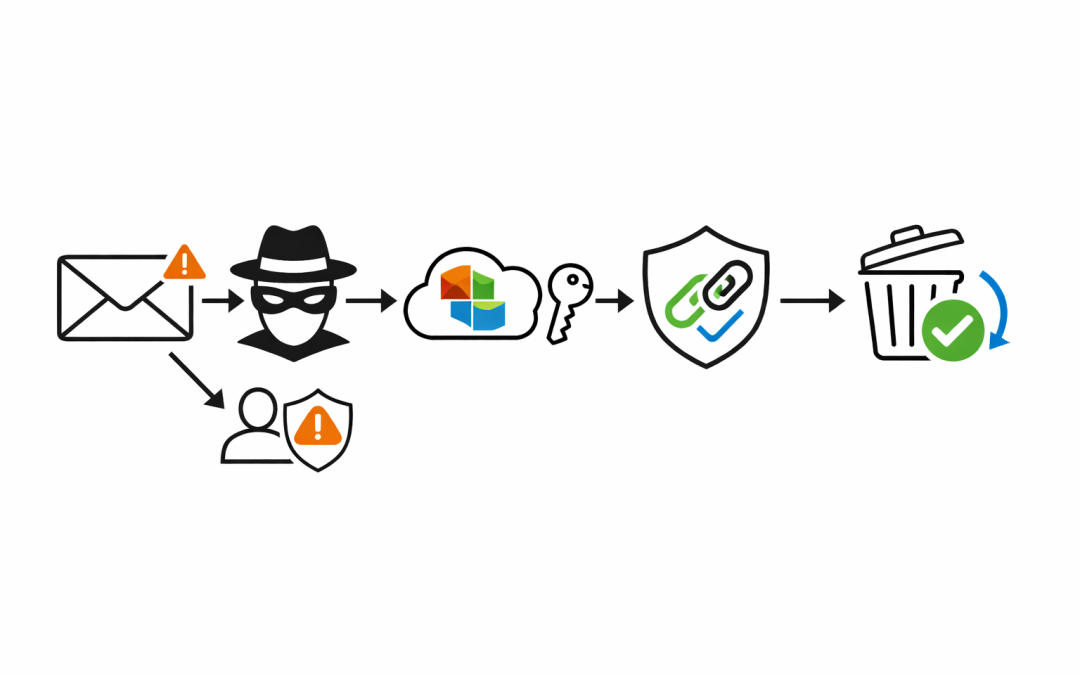
Most phishing discussions still focus on user awareness. That matters, but it is not enough. The real issue for most Australian businesses is that phishing is no longer just a bad email with poor spelling. It is impersonation, credential theft, malicious links that...