by CPI Staff | Apr 24, 2026 | Blog, Microsoft 365, Microsoft Intune, Windows 365
Too many IT teams are still managing endpoints through three different operating models at once. Physical laptops sit in one stack, remote access sits in another, and virtual desktops sit somewhere else again. That fragmentation is expensive. It slows onboarding,...
by CPI Staff | Apr 22, 2026 | Blog, Cybersecurity, Essential 8, Microsoft 365 Security, Microsoft defender XDR, Microsoft Intune
For years, Australian IT leaders treated macOS as the “quiet corner” of the fleet. A handful of executives and designers on MacBooks, a sprinkle of engineers, and a general assumption that Apple’s built-in protections were enough. That assumption no...

by CPI Staff | Feb 23, 2026 | Blog, Microsoft 365, Microsoft Intune
In this blog post 5 Signs Your Current IT Provider Isn’t Keeping Up in 2026 we will look at the warning signs that your IT partner is quietly falling behind—and what that means for cost, security, productivity, and compliance. If you’ve found yourself thinking, “We’re...

by CPI Staff | Feb 1, 2026 | Blog, Microsoft Intune
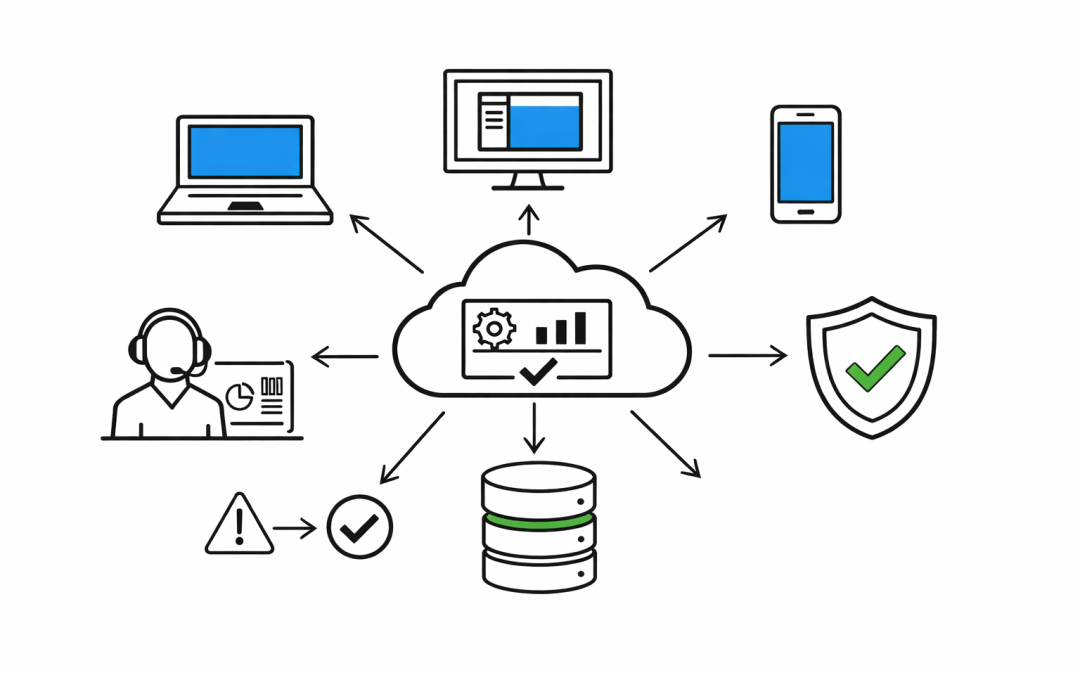
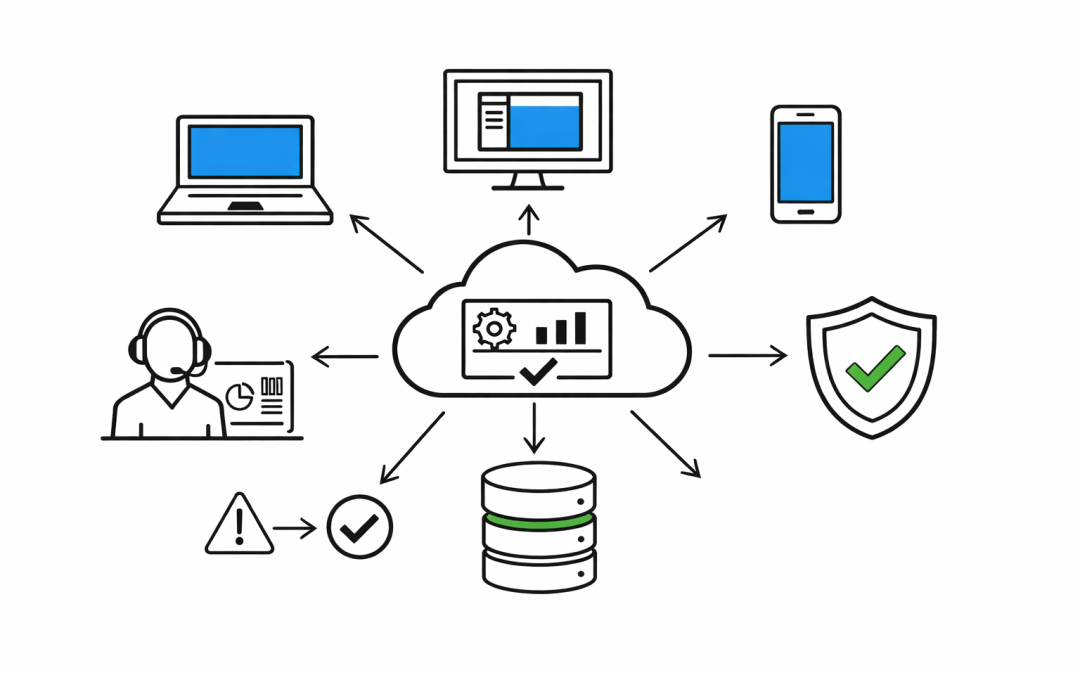
In this blog post Enforce Device Compliance with Microsoft Intune for Safer Access we will walk through how to use Microsoft Intune to define “good device hygiene,” measure it continuously, and then enforce it at sign-in time. The goal is simple: let productive work...

by CPI Staff | Jan 29, 2026 | Blog, Microsoft Intune
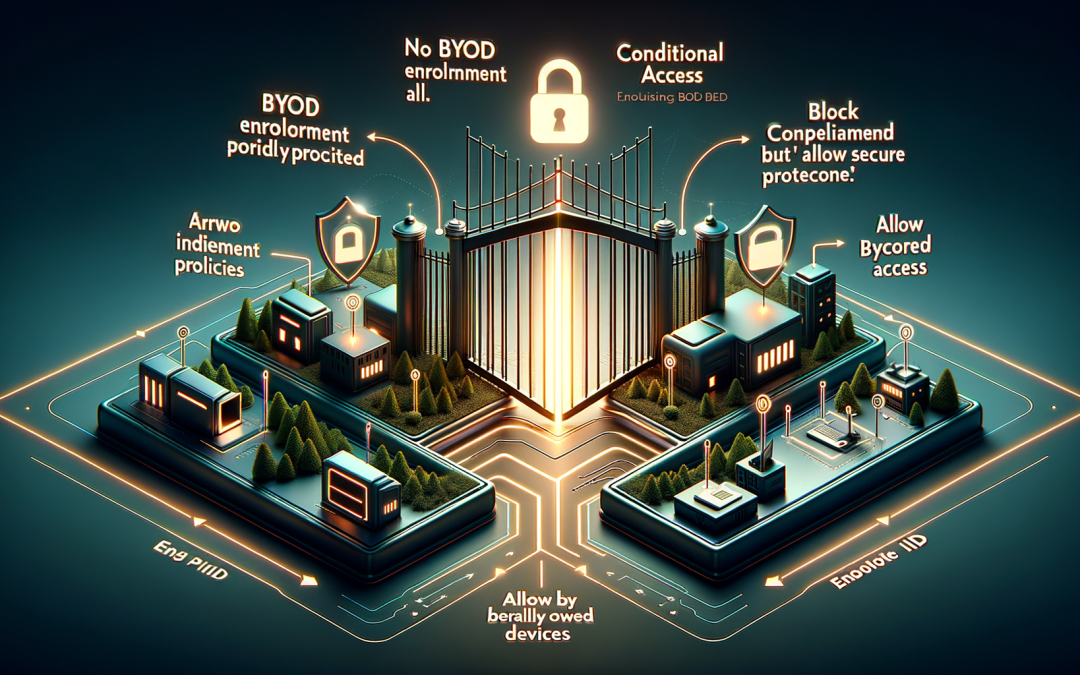
In this blog post Block Personally Owned Devices with Microsoft Intune for Better Security we will explain how to stop personally owned devices (BYOD) from enrolling into Intune, why it matters, and how to do it safely without breaking legitimate business workflows....

by CPI Staff | Jan 29, 2026 | Blog, Microsoft Intune
In this blog post Intune Device Type Restriction Policies Explained for IT Teams we will walk through what device type restriction policy is in Microsoft Intune, why it matters, and how to configure it in a practical way. At a high level, Intune device type...