by CPI Staff | Feb 6, 2026 | Blog, OpenAI
In this blog post GPT-5.3 Codex Released What IT Teams Should Do Next we will break down what GPT-5.3-Codex is, why it matters for modern engineering teams, and the practical steps you can take to evaluate it safely and productively. 🎧 Listen to This Article...

by CPI Staff | Feb 6, 2026 | Anthropic, Blog
In this blog post Claude Opus 4.6 Released What IT Teams Should Do Next we will walk through what Claude Opus 4.6 is, what actually changed, and how to evaluate it for real production use across dev, ops, and enterprise knowledge workflows. Claude Opus 4.6 is...

by CPI Staff | Feb 5, 2026 | Blog, GitHub, GitHub Copilot CLI, GitHub Copilot SDK
In this blog post GitHub Copilot CLI vs GitHub Copilot SDK we will break down what each option is, how they work under the hood, and when to use one, the other, or both. If you’re an IT leader planning governance or a developer trying to speed up delivery, the key is...

by CPI Staff | Feb 5, 2026 | Blog, GitHub Copilot SDK
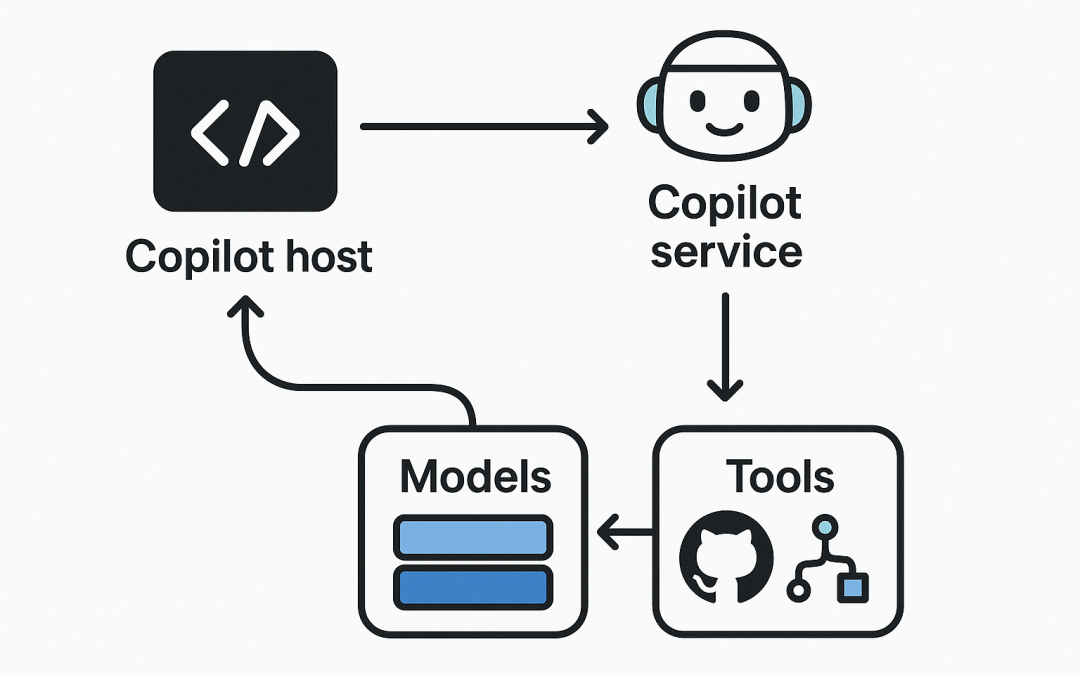
In this blog post GitHub Copilot SDK Architecture Explained for Teams and Builders we will walk through the moving parts that make Copilot integrations work, and how to design them so they stay secure, maintainable, and useful for real teams. At a high level, GitHub...

by CPI Staff | Feb 5, 2026 | Blog
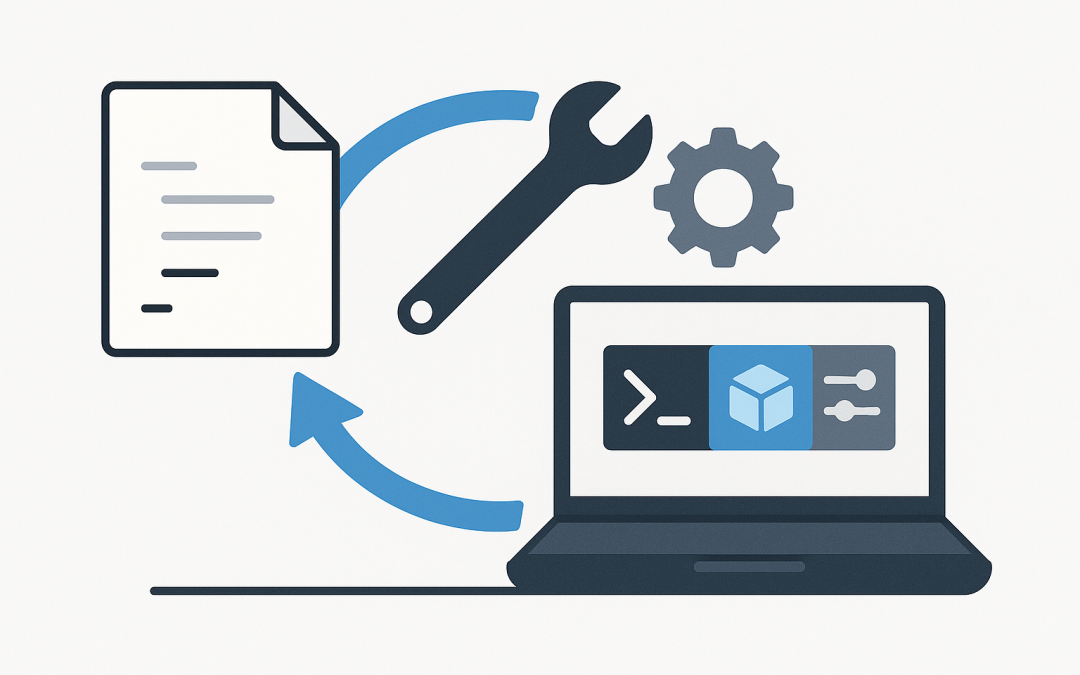
In this blog post Automate Dev Machine Setup with WinGet Configuration on Windows we will walk through how to turn a brand-new Windows laptop into a ready-to-code dev machine using a single, repeatable command. If you’ve ever copied a checklist from Confluence,...

by CPI Staff | Feb 5, 2026 | Blog, LLM
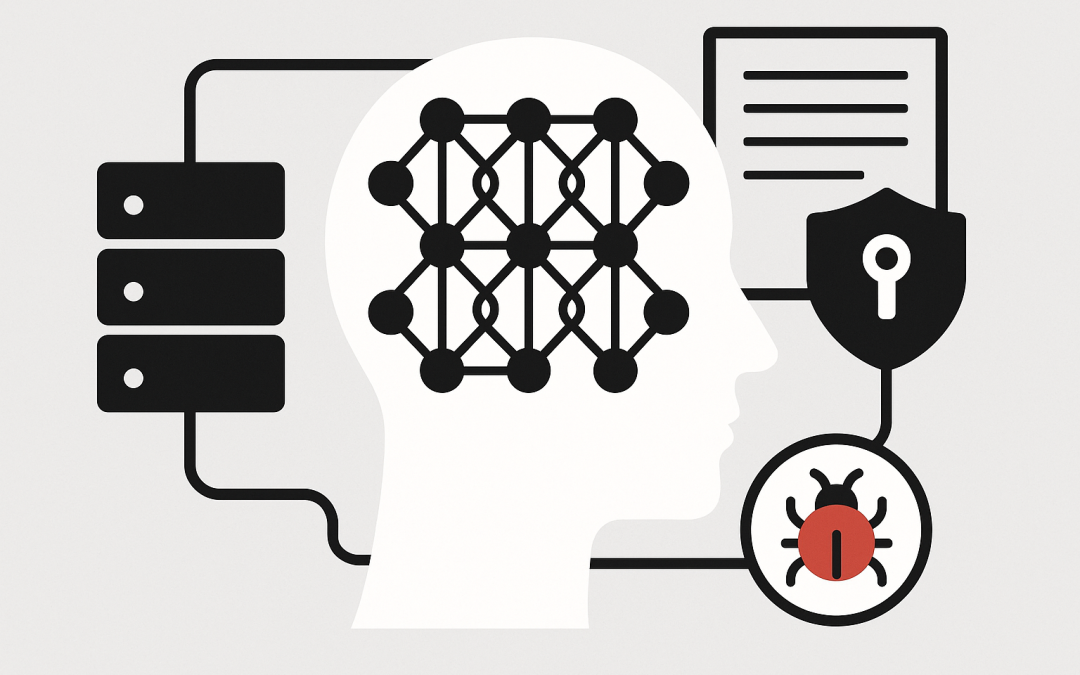
In this blog post Detecting Backdoors in Open-Weight LLMs Practical Steps for Teams we will walk through a pragmatic approach to finding hidden “sleeper” behaviours in open-weight language models before they reach production. Detecting Backdoors in Open-Weight LLMs...